Mozilla Firefox Blocks Malicious Add-ons Used by 455K users
Mozilla Firefox’s development team has blocked several malicious add-ons that are installed by about 455,000 users.
The development team said that back in June, the team discovered that some of the malicious add-ons were exploiting the Proxy API to block Firefox updates.
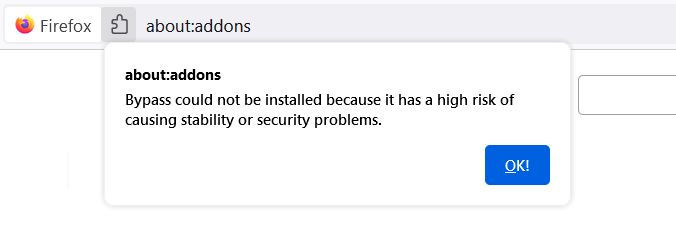
Now, these malicious add-ons have been blocked by the development team.
The Proxy API was being used by the add-ons named Bypass, and Bypass XM to initially intercept the request and then redirect those web requests.
The redirection is done so as to block the users from downloading any updates, updating the remotely configured content, and lastly restricting access to updated blocklists.
Mozilla’s Rachel Tublitz and Stuart Colville said that the approvals for new add-on submissions that use the Proxy API are halted until a fix for the same is released for users.
The approvals will be halted for the time being so as to avoid any more of the users getting affected by the new add-ons that abuse the proxy API.
Meanwhile, Mozilla will incorporate changes to harden the update process starting Firefox 91.1 version. A fallback mechanism to direct connections for the update purposes, as well as the other important requests initiated by the browser, has been deployed.
This means that the downloads will always take place no matter if the proxy configuration causes connection issues or not.
Mozilla has even added a system add-on named Proxy Failover that will block similar malicious add-ons that try to exploit the Proxy API.
This system add-on is hidden within the browser and Firefox has made it practically impossible to disable it.
Mozilla hasn’t given any statement on whether two add-ons were doing anything else malicious other than exploiting the Proxy API.
Table of Contents
Update Firefox Browser to Latest Version
Meanwhile, Mozilla is suggesting its users update their browsers to the latest version (Firefox 93). Updating to the latest version will give assurance that they are secured from the add-ons exploiting the proxy API.
Rachel Tublitz and Stuart Colville further said that regularly updating the Firefox browser plus using the Microsoft Defender on Windows OS is a good practice. Defender and Firefox 93 collectively help secure your system against this issue.
As per the free online virus, malware scanning service ‘VirusTotal’, Microsoft Defender is the only anti-malware solution that is detecting the add-ons as malicious.
Microsoft has tagged the add-on malware as BrowserModifier:JS/BypassPaywall.A.
Try to update your browser to Firefox 93 as it contains an updated blocklist that blocks these malicious add-ons.
In case, you are unable to update the Firefox, you have an alternative option i.e: to search and remove the add-ons that limit you from upgrading.
For better insights on how to search and remove the add-ons, follow the below-mentioned steps:
- First step is the go to the Troubleshooting Information page.
- Now, go to Add-ons section. Then, search one of the following entries with the help of search toolbar in extension page:
Name: Bypass
ID: {7c3a8b88-4dc9-4487-b7f9-736b5f38b957}
Name: Bypass XM
ID: {d61552ef-e2a6-4fb5-bf67-8990f0014957}
Match the above-mentioned IDs with the search results, if you don’t find any of these IDs in your list, you aren’t affected by the issue.
Additionally, if you like to start from scratch, you can download the latest version of Firefox.
Citation
Are you looking for more software news? Stay tuned for the latest software news from top tech industries.




