Security researchers at Palo Alto Network’s Unit 42 declared that they have found this week ‘PGMiner’, a cryptocurrency mining botnet that targets PostgreSQL databases running on Linux.
PGMiner, the botnet is yet another cybercrime operation that is designed to target weak PostgreSQL databases for fiscal benefits.
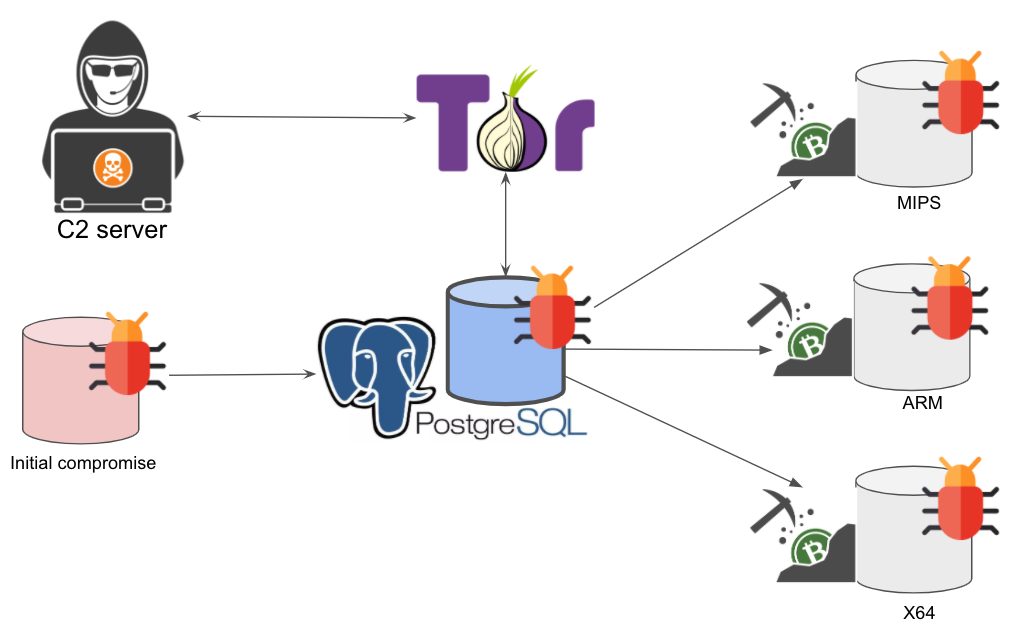
As per the statement by researchers at Palo Alto Networks, the botnet operates by exploiting a disputed PostgreSQL remote command execution vulnerability that jeopardizes database servers for cryptojacking. PGMiner tries to connect to the mining pool to illegally mine for Monero.
Target PostgreSQL
In the initial stage of the attack, the botnet tries to guess the passwords for the PostgreSQL account with brute-force methods. If the credentials are not strong, the malware can obtain access at the initial stage itself.
On guessing the password precisely, the PGMiner tries to exploit a remote code execution vulnerability named CVE-2019-9193.
In case the owners of the PostgreSQL database have forgotten to disable the users or forgotten to change the credentials of the account, then the hackers will be able to obtain access to the database and utilize the PostgreSQL COPY from PROGRAM feature to increase their access to the database app to the underlying server and obtain access to the entire OS.
On getting a better hold of the compromised system, a crypto mining tool is deployed by the PGMiner team so they could try to mine as much Monero crypto as they can before they get caught or exposed.
As per the report from Unit 42, at the time of the report the botnet just had the capability to deploy miners in Linux MIPS, ARM, and x64 platforms.
It is said that the botnets are controlled through a command and control (C2) server which is hosted on the Tor network.
The previous month, Delaware County, Pennsylvania has paid a total of $500,000 in ransom after their systems were affected by the DoppelPaymer ransomware.
Subscribe to our newsletter for the latest security news right from the security and research industries.




